📌 MAROKO133 Update crypto: Justin Sun Offers to Negotiate With KelpDAO Hacker Afte
Tron founder Justin Sun publicly called on the KelpDAO bridge hacker to negotiate a return of the stolen funds, warning that a $292 million loss could bring down both Aave and KelpDAO.
Sun’s appeal followed the largest Decentralized Finance (DeFi) exploit of 2026, which drained 116,500 rsETH from KelpDAO’s cross-chain bridge on April 18.
Sun Moves Funds as Aave Takes the Hit
The attacker exploited a flaw in KelpDAO’s LayerZero-powered bridge, forging cross-chain messages to release rsETH without corresponding token burns.
The stolen tokens were then deposited as collateral on Aave V3, where the hacker borrowed large volumes of Wrapped Ether (WETH) against them.
Because the rsETH became unbacked, the positions are effectively unliquidatable, leaving Aave with over $236 million in bad debt.
Aave froze rsETH markets on both V3 and V4 within hours. Aave founder Stani Kulechov confirmed the exploit originated outside Aave’s contracts.
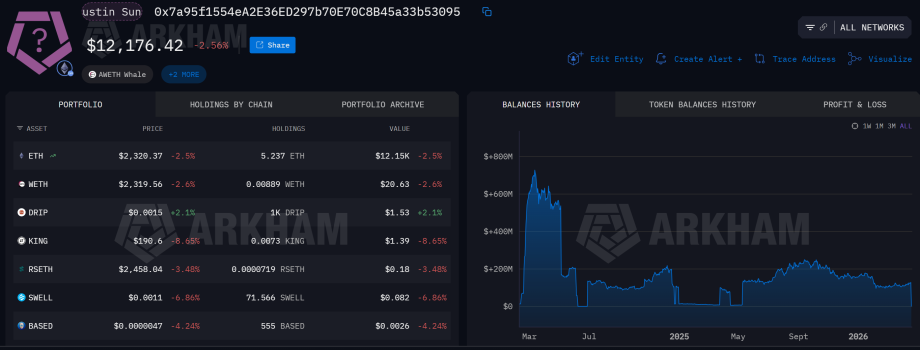
On-chain data shows Sun urgently withdrew 65,584 ETH, worth roughly $154 million, from Aave and deposited it into Spark shortly after.
His total Aave exposure has reportedly dropped to $380 million, while his Sky and Spark holdings have risen to $2.13 billion.
“OK — Kelpdao hacker, how much you want? Let’s just talk. With KelpDAO’s help, of course. It’s simply not worth it to sacrifice both Aave and KelpDAO and let them go down over this hack,” wrote Justin Sun in a post.
Interoperability protocol Axelar also responded, expressing solidarity with LayerZero and urging the industry to adopt stronger bridge security standards.
Axelar pointed to the importance of multi-validator configurations, noting that Kelp’s single-validator setup may have enabled the breach.
The exploit overtakes the $285 million Drift Protocol hack from April 1 as the largest DeFi loss this year.
The post Justin Sun Offers to Negotiate With KelpDAO Hacker After $292 Million Exploit appeared first on BeInCrypto.
🔗 Sumber: www.beincrypto.com
📌 MAROKO133 Eksklusif crypto: Ethereum Foundation-Backed Program Exposes 100 Nort
The Ketman Project, operating under the Ethereum Foundation’s ETH Rangers security program, has in the latest Ethereum news, identified approximately 100 North Korea Crypto IT operatives embedded inside Web3 companies using fabricated identities, the result of a six-month investigation that ended with one of the most detailed public tallies of DPRK insider infiltration in the sector’s history.
The threat model has shifted. Where North Korea’s state-level crypto operations once centered on remote exploits and exchange hacks, the 2025 pattern is coordinated workforce infiltration, operatives passing HR screenings, accessing internal repositories, and sitting inside product teams for months before detection.
- Operatives identified: ~100 DPRK IT workers found using fake identities inside Web3 firms
- Investigation duration: Six months, conducted by the Ketman Project with ETH Rangers support
- Program scope: ETH Rangers funded 17 independent researchers, recovered or froze $5.8M in exploited funds, traced 785+ vulnerabilities, handled 36 incident responses
- DPRK theft scale: $2.02 billion stolen in 2025 alone – a 51% increase from 2024 – pushing cumulative haul to $6.75 billion
- Drift Protocol hack: DPRK-linked attackers executed a $285 million exploit on April 1, 2026, the largest DeFi hack of the year
- Real-world case: Exchange Stabble issued a withdrawal alert after a DPRK IT worker infiltrated its leadership team
- Watch: Investigators are actively tracking Drift exploit proceeds; regulatory scrutiny on DeFi employment vetting expected to intensify
Discover: The best crypto to diversify your portfolio with
Ethereum News: How the ETH Rangers Crypto Investigation Actually Worked – and What 100 North Korea Operatives Really Means
ETH Rangers launched in late 2024 through a partnership between the Ethereum Foundation, Secureum, The Red Guild, and the Security Alliance (SEAL), deploying 17 independent security researchers across a six-month mandate to strengthen the Ethereum ecosystem defenses.
The Ketman Project was one of those funded efforts, and its output went well beyond the typical audit or bug bounty scope.
Identifying 100 operatives means matching fabricated identities to known DPRK tradecraft patterns: inconsistent work histories, communication behaviors suggesting time-zone masking, payment routing through specific intermediaries, and technical fingerprints that recur across unrelated applicants. That’s intelligence work, not just security research.
It requires sustained monitoring across job boards, GitHub activity, hiring pipelines, and behavioral signals inside existing teams.
The broader ETH Rangers program delivered material results beyond the Ketman work: participants recovered or froze over $5.8 million in exploited funds, traced 785+ vulnerabilities and proof-of-concept exploits, ran 36 incident responses, and delivered more than 80 security training sessions.
Open-source outputs included a DeFi incident analysis platform, a GitHub suspicious account detector, and a client-side DoS testing framework.
That GitHub tool is relevant here. Suspicious account detection is precisely the capability needed to surface DPRK-linked developers operating under cover – accounts with manufactured contribution histories, coordinated activity patterns, or anomalous repository access. The Ketman findings likely drew on exactly this tooling.
What “100 operatives” doesn’t mean: that those individuals were necessarily running exploits in real time. DPRK IT worker infiltration serves multiple functions: revenue generation for the regime through legitimate salaries, intelligence collection on protocols and codebases, and pre-positioning for future attacks.
The immediate financial damage may be limited; the long-term exposure is structural.
Discover: The best pre-launch token sales
The post Ethereum Foundation-Backed Program Exposes 100 Nort Korea Operatives Infiltrating Crypto Firms appeared first on Cryptonews.
🔗 Sumber: cryptonews.com
🤖 Catatan MAROKO133
Artikel ini adalah rangkuman otomatis dari beberapa sumber terpercaya. Kami pilih topik yang sedang tren agar kamu selalu update tanpa ketinggalan.
✅ Update berikutnya dalam 30 menit — tema random menanti!